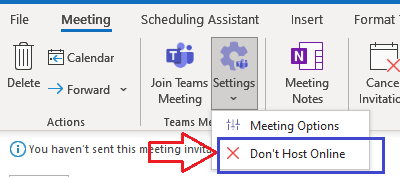
Following on from this post:Office 365 Migrations - What happens to Outlook Meetings with embedded Teams URLs? - Nero BlancoWe developed a tool to strip out Teams info from Calendar invites, so that new Teams info co...
Most popular posts:
Uninstall Microsoft Teams cleanly
Teams Cache CleanerTry this one last time...Start PowerShell as Admin and run:Set-ExecutionPolicy -ExecutionPolicy RemoteSigned -Scope Processtaskkill /IM teams.exe /F /TGet-ChildItem -Path ([System.Environment]:...
Where do emails sent to the default Microsoft Teams email address go?
Where does the default Teams email go?When you first create a Microsoft Team it allocates an email address for the Team. That email address is built by the Display Name (with spaces and special characters remove...
Intune -Troubleshooting and Learnings
We are rolling out Intune Compliance and Configuration Policies. MDM (Enrolled) for corporate devices and MAM (unenrolled) for Personal devices. We are using MDM and MAM to rollout (Windows Information Protection) WIP. We are not using Config Manager, and all devices are Azure AD Hybrid Joined. This blog focusses on Windows 10 devices and does […]
Guest Account conflicts with Exchange Online
Guest Accounts not receiving email notifications In truth, this blog could have been called anything. Probably the Guest Account dilemma, but I have used that kind of title a few times now, none the less – it is a dilemma. This is a blog I have been wanting to write for ages, because it has […]
Whiteboard in Office 365 and Teams
We were asked to investigate an issue for a client today where the Whiteboard app wasn’t available to Teams users in a Teams meeting. Here are the key requirements for enabling Whiteboard: Enable Whiteboard for tenant License the users Enable the Teams Policy Apply the Teams Policy to users Enabled Whitebard for the tenant. Head […]
OneDrive for Business Reconfiguration
Office 365 – Tenant to Tenant Migrations OneDrive for Business Reconfiguration Today I’m going to briefly outline Reconfiguring the OneDrive for Business Desktop Application. I say briefly because as a departure from some of our other blogs I’m going to depart from the usual step by step process with screenshots. If you have landed here, […]
Case Study:- HSBC
PDF version of the case study. Otherwise, please continue to find full text below. Improve Productivity and Enterprise Mobility Globally by Building and Supporting Email Migration Systems Nero Blanco partners with HSBC to migrate more than 270,000 mailboxes to deliver improved collaboration EXECUTIVE SUMMARY As one of the world’s largest banking and financial organisations, HSBC […]
Guest account sign in blocked
Recently we gave a customer access to a team in our tenant, we conduct a lot of B2B collaboration. As you know from my previous Guest account blog, this initially creates the individual in our tenant as an “Invited user” (Guest), then, once they accept the invitation, and accept that Nero Blanco can read their […]
Microsoft Office 365 Security Health Check
A simple traffic light report, produced by one of our Office 365 Consultants, looking into your configuration to highlight if there are any areas of concern and to give you an increase comfort level that you have a good security posture
Hmmm…can’t find that team
We’re seeing renewed issues with Microsoft Live ID or Microsoft Personal accounts interfering with new corporate identities when an organisation starts is Microsoft Cloud/Teams journey. Users cannot access resources (documents/Teams) which they have been given permission, or join Microsoft Teams due to security restrictions, like conditional access or guest account settings. Conrad provided an excellent […]
Troubleshooting Microsoft Teams Logon
This is a bit of a sledgehammer to crack a nut scenario to get you back up and running on teams. Where we have had to use this is for Tenant to Tenant migrations where the user and their workstation simply wont connect to the new tenant, and it is persistent to the legacy tenant. […]
Leaving a Team outside your Organization
Ever had that situation where you collaborate with an external organization and that project/collaboration comes to its natural (or unnartural0 conclusion, but then you are left with their organization cluttering up your Teams organizations drop down? Not the end of the world of course, but annoying none the less, and if you like a clean […]
PowerShell Get-History
One command that I love to use in PowerShell is Get-History. It retrieves all of the commands that you have run in this session. You can use the id and count parameters to pick a single command or a number of commands including and prior to the id e.g. Get-History -id 10 -count 5 gets […]
Working with Saved Messages in Microsoft Teams
Microsoft Teams is revolutionising how we communicate with a company. It speeds up working together, allows fast collaboration and retains business knowledge within a place that isn’t lost when someone leaves the organisation. One problem though is information overload and managing which conversations you still need to get back to…! Luckily you can mark a […]