Tenant Governance & Compliance
Data governance is part of IT at the enterprise level. It serves as regulatory compliance, and is part of a business strategy to protect the integrity of the data estate.
When data resides in multiple tenants there can be a security or data leakage exposure if the policies and settings are not aligned with the corporate standard.
Compare periodic configuration snapshots to ensure governance of changes and maintain tenant compliance. Even across multiple tenants
Our solution is here to help, compare or track your tenant settings.
Single tenant configuration snapshot
We perform frequent scans of your tenant and sends out a report detailing the changes that have occurred in the given time frame. This might be a configuration change made by an admin, or it could even be a new parameter surreptitiously add into the tenant by Microsoft 365.
Nero Blanco tenant tool will take a snapshot of the tenant configuration, then another at a later date. A comparison of the two data sets will be made to provide a delta report so you can understand any configuration drift. All key workloads are covered, and all parameters which can be access by PowerShell are included, along with many settings throughout the Azure AD blades and Graph.

Multi-tenant configuration
We can also compare multiple tenant configurations, this is very useful in mergers and acquisitions to understand differing configurations and security postures. Furthermore, it is also useful in creating development or test environment when trying to replicate the production configuration.
At Nero Blanco we especially use this tool in tenant to tenant (T2T) migrations so the customer understands how, for example, the user experience might be impacted, internally and for perhaps guests.
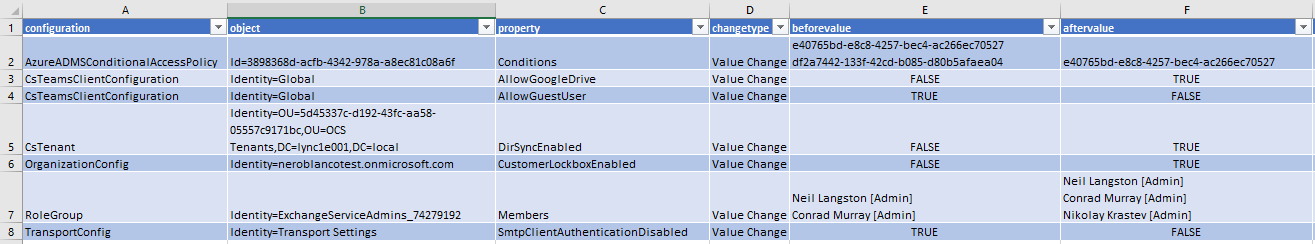
For example, here is a test tenant where we have made some changes.
- We removed a group from a conditional access policy exclusions list.
- Updated Teams to allow Google Drive use, but disallow Guests
- Dirsync has been enabled on the tenant, and so has the customer lockbox.
- An additional admin was added into the Exchange service admins role group.
- SMTP client authentication is now allowed.

Insights
To have reliable and auditable insights into the Microsoft 365 tenant configuration, along with the changes within is a great security control. This allows a consistent configuration management solution to harmonise one or more tenants.
We do not scan device, users or groups, teams, guest or mailbox configurations, this serves little advantage and creates noise when looking at the deltas between configuration collections. However, if there are critical resources which need to be monitored we can add them by request.
The difference between two tenants can be profound, especially at different maturity levels. We will work with you to create a mapping to align configuration items between the tenants to reduce the noise our comparison tool produces. For example; if a conditional access policy performs the same actions in two tenants but only has a different name, we will still compare and report on any configuration change however not alert on the name difference.
Contact us below for further information.
