Large tenant‑to‑tenant (T2T) migrations are complex, multi‑workload programmes that touch every layer of Microsoft 365. Over time, recurring patterns and lessons emerge, especially when dealing with thousands of users, legacy configurations, holds, storage constraints, and identity dependencies. Below are some of the most valuable lessons we’ve learned from delivering large‑scale M365 migrations. Lesson 1: Active […]
Providing expert migration services during Mergers & Acquisitions
Most organisations only migrate to Microsoft 365 once or twice in their lifetime. For us at Nero Blanco IT, it’s something we do every week. For over 15 years we’ve helped organisations of every size move to Microsoft 365 safely, securely and with minimal disruption. Nero Blanco migration experience15+ years delivering Microsoft migration projectsHundreds of […]
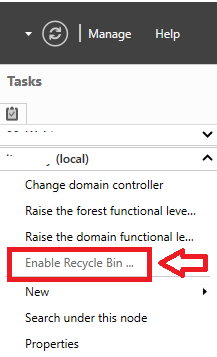
Working with the on-premises AD Recycle Bin
Generally in day to day identity management you would not often need to resort to the Active Directory Recycle Bin, but when you do, typically it is a high priority request and you find yourself having to reacquaint yourself with the commands you need. Accidental deletion scenarios Where we have seen the need to restore […]
Active Directory: Source has exceeded the tombstone lifetime
I was working with a client recently who had various Active Directory replication issues. They had a multi-domain forest in Windows Server 2008 R2 functional levels. Now the two fundamental errors were DNS zones duplicated between the domains (including the zones used by the subdomains) Network firewalls between the domain controllers One big call out […]
Inside Kerberos – 7: Wrap up
Alright, we’ve covered a lot of ground, but let’s wrap up by grabbing our original questions and answering the 1. Why is there a problem with SIDHistory and Domain Local Groups, and exactly what is the problem? We’ve seen that Domain Local groups can have sid-history applied from one domain to another, this allows for […]
Inside Kerberos – 6: Conversations
We have covered a lot of ground so far, and we have touched on the Kerberos conversations that go on, but let’s take a deeper look at exactly how these messages are made up and how they are protected. Elements to protect the transmission Secret Keys Secret keys are stored inside the Security Account Manager […]
Inside Kerberos – 5: Tokens
Alright then, we’ve covered SIDs, SIDHistory, and Tickets. Let’s move onto Access Tokens. Privilege Access Certificate The Privilege Access Certificate or PAC is a Microsoft extension to Kerberos utilizing the Authorization Data field in the tickets. This is sometimes referred to as the Access Token, however strictly speaking the Access Token is the structure generated […]
Inside Kerberos – 4: Tickets
Ok I think we have talked enough about SIDs in the previous two parts on SIDs and SIDHistory. Let’s move on to Kerberos tickets… Luckily in Kerberos there are really only two tickets (which confusingly are sometimes also referred to as Tokens) Ticket Granting Ticket (TGT) Service Ticket (ST) Both of these tickets are issued […]
Inside Kerberos – 3: SIDHistory
In this blog we will be exploring SID History, and it follows on from Part 1 which gave an overview of Kerberos, and Part 2 which was all about SIDs. The attribute sid-history has been there right since Windows 2000 and is used to store all of the SIDs that an object has had. […]
Inside Kerberos – 2: SIDs
In Part 1 we set the scene in regards to how Kerberos works at a high level, so let’s now get down and dirty with Security Identifiers (SIDs) What is a Security Identifier (SID)? From MSDN: “A security identifier (SID) is a unique value of variable length used to identify a trustee. Each account has […]
Inside Kerberos – 1: Overview
I recently did some work at a client to help migrate them to a new Active Directory. While setting up the migration including password and SidHistory syncs I told them to be careful of Domain Local Groups which can cause issues if users are nested directly in them. Now I knew this was true, but […]
The Groups Dilemma – post migration
Today a client that we had previously migrated off Lotus Notes asked us about applying Groups to their Shared Mailboxes in Office 365 but ensuring that the Shared Mailbox Owners had the ability modify those Groups to provide access. This blog very much goes hand in hand with this blog I wrote on Shared Mailboxes, […]